The only constant is change.
Someone said that there can’t be a Web 2.0 because there was never a Web 1.0. In like fashion, do you remember when George W. Bush said “Internets” and everyone laughed? It turns out, however, that he was right: there are, indeed, Internets (i.e., plural as in more than one). 1
My personal dissatisfaction with the term Internet
I think that the term “Internet” is a very poor way to describe the service that we use when we go online and what we actually do when we’re in virtual space. That’s because when we go online, we: upload, download, chat, read, write, talk, watch movies, listen to songs and learn. In fact, we perform what can be called the essence of communication.
The next-generation Internet
If the only constant is change then it stands to reason that the Internet, like everything else, is also subject to evolution. If it is subject to evolution then we needn’t split hairs about what we call it. It’s no longer a matter of appellation, but of functionality. It’s not what we call the thing (or, service), but what the thing (or, service) does for us that counts.
There’s much in a name
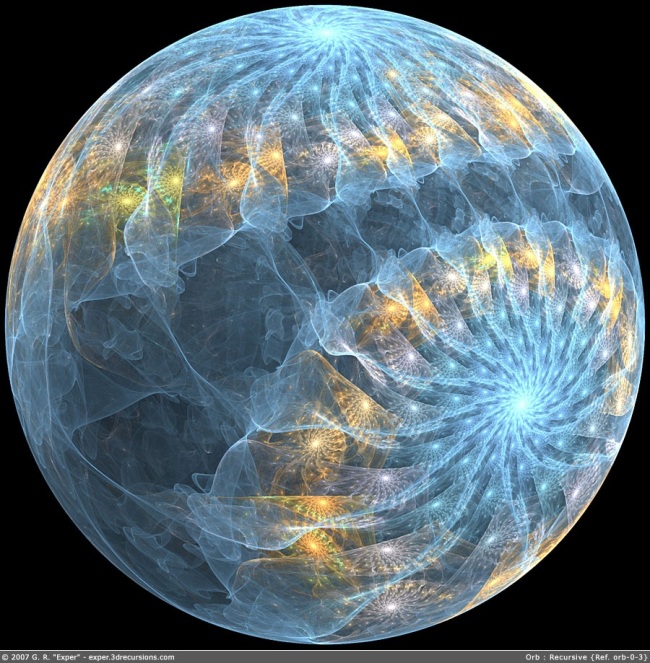
Having said that, names are, nevertheless, important. Imagine for a moment that the Internet were called ITECS. ITECS stands for Interactive Total Expression Communication Sphere. Interactive because the Internet implies movement and interactivity; Total because of the all-encompassing scope of material available online; Expression because, in toto, everything on the Internet is an expression of some kind; Communication because what we express is non-static and, via interactivity, reaches intended recipients; and Sphere because I think this sounds so much better than Internet or, Information Super Highway which implies a linear trajectory as opposed to something more holistic like ITECS.
ITECS
Today, we have Internet1 (See, footnote 1): a hodge-podge of information that is slow to access and may or may not be accurate. (See, Static and Closed versus Interactive and Open Internet Web pages, lubarascheff.com) with a division of functions (See, Get to the Point: Effective Communication in the Digital Age, lubarascheff.com).
But what will next-generation ITECS be like?
Falling into the realm of speculation
Let’s do a free fall into the realm of speculation. Let’s imagine a bit and make some smart guesses. Unlike Internet1 (and more like Internet2), ITECS will be fast; much faster than what we’re using today (whether Internet1 or Internet2). It will be entirely wireless and perhaps somehow connected to our bodies (See, Do As the Toltecs, lubarascheff.com, where I discuss screen incorporation) and resolution will be higher than anything extant. ITECS will be transparent. The case can be argued that in a speedy and transparent ITECS, users will be able to almost instantly do the following: obtain information they seek; express themselves; and share information they deem valuable with a close group of friends or the world. With speed, ease of access and a more evolved mindset that will necessarily accompany a more evolved ITECS, there will be less of a perceived need to dissimulate and/or deliberately upload incorrect information onto ITECS. (See, “Internet inaccuracies” in Static and Closed versus Interactive and Open Internet Web pages, lubarascheff.com). Users themselves will, together, act as a kind of counterbalancing “correction mechanism” if this happens.
In the same way that when we think it, our brains send signals to our fingers and toes that cause them to move, ITECS will enable us to, when we wish, holistically “merge” with its worldwide community of online users. It will be an open, transparent, fast, ultra-high resolution, self-regulating sphere of total, interactive, information exchange. ITECS will meet the needs of all users without being detrimental to people or the planet.
Evolution and credibility
Why should we wait for information? If Internet2 “moves data 100 to 1,000 times faster than the old-fashioned Internet [i.e., Internet1],” 2, ITECS will move data at nearly the speed of thought. I say nearly because, even though hyperly minimzed, as futurist Dr. Kaku posits (See, The Zero-Sum Game, lubarascheff.com), technical components (i.e., microchips) will still exist. ITECS will, therefore, be almost instant. Frustration gone. Almost instant access to what you need most at the moment you need it. Doesn’t this sound great?
When will this happen?
ITECS (or, something similar only called by a different name) will arrive sooner than we think. This is because it will come into existence based on needs defined by our evolving communication requirements. Our collective, evolving needs will compel innovators to create ITECS.
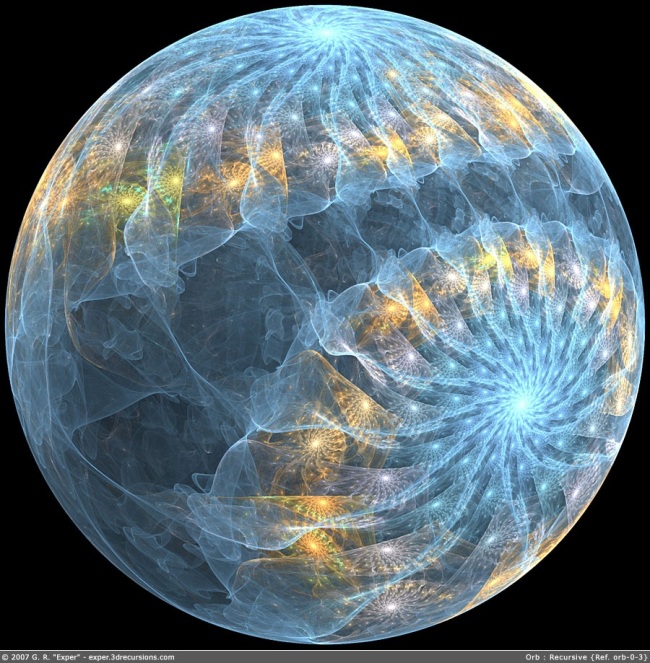
Orb: Recursive
Author: “Exper” Giovanni Rubaltelli, Abstract Design, (c) 2007 G.R. “Exper”–exper.3drecursion.com
References
1 Russo, Alexander. Slate. Internet2: It’s better, it’s faster. You can’t use it. Posted on Tuesday, June 7, 2005. Accessed on Saturday, August 10, 2013. http://www.slate.com/articles/technology/webhead/2005/06/internet2.html. And, Urban Dictionary, Definition of “Internets.” Accessed on Saturday, August 10, 2013. http://www.urbandictionary.com/define.php?term=internets&r=related.
2 Russo, Alexander. Slate. Internet2: It’s better, it’s faster. You can’t use it. Posted on Tuesday, June 7, 2005. Accessed on Saturday, August 10, 2013. http://www.slate.com/articles/technology/webhead/2005/06/internet2.html.
ITECS: THE NEXT-GENERATION INTERNET Copyright © 2013 Luba Rascheff